Zero-Knowledge Governance: When the State Verifies Without Knowing

The 2030 Scenario
Imagine walking into a polling station in 2030. You cast your vote for the next mayor, receive a tamper-proof receipt, and leave. At no point did any official verify your identity by looking at your ID card. At no point did any system record who you voted for. Yet the election was completely secure, fully auditable, and immune to fraud.
Or consider filing your taxes. You prove your income qualifies for certain deductions without revealing your exact salary. You demonstrate you’re eligible for healthcare subsidies without disclosing your medical history. You verify your age to purchase restricted goods without showing your birth date.
This isn’t science fiction. This is the promise of zero-knowledge governance—and it’s closer than you think.
SECTION I: The Verification Paradox
For centuries, verification meant revelation. To prove you were eligible for something, you had to expose information about yourself. The more sensitive the service, the more intrusive the disclosure.
This paradigm created a fundamental tension that has plagued both public and private sectors: How do we deliver personalized services without accumulating dangerous amounts of personal data?
The traditional answer—“trust us with your data”—is collapsing under the weight of breaches, surveillance scandals, and regulatory pressure. Enter zero-knowledge proofs (ZKPs), a cryptographic innovation that separates verification from revelation.
What is a Zero-Knowledge Proof?
At its core, a ZKP allows one party (the prover) to prove to another party (the verifier) that a statement is true, without revealing any information beyond the validity of the statement itself.
The classic analogy involves two balls and a colorblind verifier. The prover claims the balls are different colors. Through a clever protocol of swapping and guessing, the verifier becomes statistically certain the claim is true—without ever learning what the actual colors are.
In governance contexts, this translates to powerful capabilities: - Prove you’re over 18 without revealing your birthdate - Prove your income is below a threshold without stating the exact amount - Prove you’ve been vaccinated without sharing your medical records - Prove you own a property without disclosing your address
Each proof is mathematically verifiable, tamper-proof, and reveals exactly zero information beyond the specific claim being proven.
SECTION II: Embedded Surveillance Meets Zero-Knowledge
Here’s where the story gets urgent. While cryptographic privacy tools mature, embedded surveillance technologies are proliferating at an unprecedented pace.
The Embedded Surveillance Reality
Modern cities are becoming sensor networks: - Smart traffic cameras with facial recognition - Acoustic sensors that detect gunshots (and conversations) - WiFi and Bluetooth scanners tracking device movements - Thermal cameras measuring body temperature and presence - Environmental sensors monitoring air quality, noise, and vibration
Individually, these sensors serve legitimate purposes: traffic optimization, public safety, urban planning. Collectively, they form a comprehensive surveillance infrastructure that would make Orwell shudder.
The Multimodal AI Amplifier
The real transformation comes from multimodal AI—systems that fuse data from multiple sources to create insights no single sensor could provide.
A camera sees your face. A microphone captures your voice. Your phone broadcasts its location. Purchase records reveal your habits. When multimodal AI correlates these streams, it constructs detailed behavioral profiles that expose not just where you’ve been, but what you’re likely to do next.
This isn’t hypothetical. Retailers already use similar technologies to predict pregnancy before family members know. Law enforcement agencies deploy predictive policing systems that anticipate crime locations. Employers monitor productivity through keyboard dynamics and application usage.
The Collision Course
We’re approaching a critical inflection point. On one trajectory, embedded surveillance and multimodal AI create a world of total transparency—where institutions know everything about citizens, but citizens know little about how they’re being watched.
On another trajectory, zero-knowledge technologies enable a fundamentally different relationship: one where services are personalized and verified, but personal data remains personal.
The choice between these futures isn’t technical—it’s political and commercial. But the window for choosing is narrow.
SECTION III: Regulatory Innovation—From Compliance to Architecture
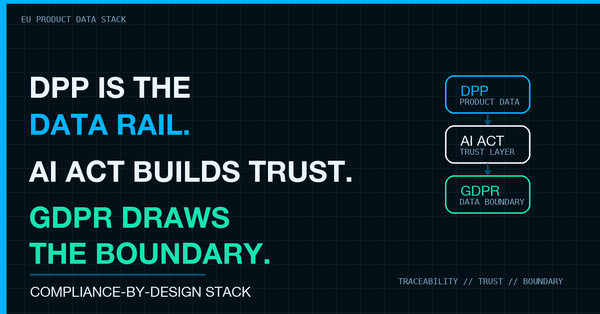
Current privacy regulations operate primarily through restriction. GDPR, CCPA, and their global counterparts tell organizations what they cannot do with personal data. They create compliance obligations, audit requirements, and penalty frameworks.
This approach has value, but it’s fundamentally reactive and incomplete. It doesn’t change the underlying architecture of data collection—it merely constrains what happens after collection occurs.
Privacy by Mathematics
Zero-knowledge governance proposes a more radical approach: changing the technical architecture so that sensitive data never needs to be collected in the first place.
This is “Privacy by Design” taken to its logical extreme. Instead of designing systems that collect data and then protect it, we design systems that simply don’t need the data to function.
Consider the difference:
Traditional Approach: - Citizen submits tax return with detailed financial information - Government agency stores and processes this data - Access controls, encryption, and audit logs protect the stored data - Breaches expose comprehensive financial profiles
Zero-Knowledge Approach: - Citizen generates a zero-knowledge proof that their tax calculation is correct - Proof cryptographically demonstrates compliance without revealing underlying figures - Government verifies the proof, not the data - No sensitive data exists to be breached
Policy Framework for ZK Governance
Transitioning to zero-knowledge governance requires coordinated action across multiple dimensions:
- Technical Standards Development
Governments should invest in open-source zero-knowledge proof systems, cryptographic libraries, and verification protocols. These are public infrastructure—like roads or the internet—and deserve public investment.
The U.S. National Institute of Standards and Technology (NIST) and similar bodies globally should prioritize post-quantum secure ZK schemes to ensure long-term viability.
- Cross-Border Verification Protocols
As data flows across jurisdictions, zero-knowledge proofs offer a path to compliance without fragmentation. A proof generated under EU standards can be verified under U.S. standards without either jurisdiction accessing the underlying data.
International standards bodies should develop interoperability frameworks for ZK credentials.
- Public-Private Partnership Models
Government agencies need not develop all ZK capabilities internally. Private sector innovation in blockchain, fintech, and secure computing can be leveraged through procurement and partnership models that require open standards.
- Transition Incentives
Organizations that adopt privacy-preserving architectures should receive regulatory benefits: streamlined audits, reduced compliance burdens, and safe harbor protections. The cost savings from reduced data breach risks should be quantified and communicated.
SECTION IV: The Enterprise Opportunity
Zero-knowledge governance isn’t just a defensive compliance strategy—it’s a competitive differentiator and innovation enabler.
Case Study 1: Financial Services
A major bank wants to offer preferential loan rates to customers with strong credit profiles. Traditionally, this requires customers to share comprehensive credit histories, income statements, and asset documentation.
With zero-knowledge proofs: - Customers prove they meet creditworthiness thresholds without revealing specific financial details - The bank verifies compliance with lending regulations without accumulating sensitive data - Regulatory audits confirm proper underwriting without exposing customer files - Data breach risks are minimized because no comprehensive financial profiles exist in the bank’s systems
Competitive advantage: Customers prefer banks that don’t require extensive financial disclosure. Regulatory compliance costs decrease. Breach liabilities diminish.
Case Study 2: Healthcare Verification
An employer wants to confirm employees are vaccinated against infectious diseases to protect workplace safety. Traditional approaches require employees to share medical records with HR departments.
With zero-knowledge proofs: - Healthcare providers issue cryptographically signed vaccination credentials - Employees generate proofs of vaccination status without revealing dates, vaccine types, or other health information - Employers verify compliance with workplace safety requirements without accessing medical records - Employees maintain complete control over their health information
Competitive advantage: Employees trust employers that respect medical privacy. HR departments aren’t burdened with sensitive health data management. Legal risks from medical record mishandling are eliminated.
Case Study 3: Supply Chain Compliance
A multinational manufacturer must verify that suppliers meet labor standards, environmental regulations, and quality requirements across dozens of countries.
With zero-knowledge proofs: - Suppliers prove compliance with specific standards without revealing proprietary business information - Auditors verify compliance claims cryptographically without accessing sensitive supplier data - Regulators confirm supply chain integrity without requiring comprehensive disclosure - Competitors cannot use compliance audits to access business intelligence
Competitive advantage: Suppliers participate more readily in compliant supply chains. Audit costs decrease. Intellectual property protection improves.
The ROI Calculation
Organizations that shift from “collect and protect” to “verify without knowing” models realize benefits across multiple dimensions:
Cost Reduction: - Data storage infrastructure: Reduced - Security operations: Streamlined - Compliance audits: Automated - Breach remediation: Minimized
Risk Mitigation: - Regulatory penalties: Lower exposure - Reputation damage: Reduced breach impact - Legal liability: Diminished data-related claims - Business disruption: Minimized security incidents
Revenue Opportunities: - Customer trust: Differentiation in privacy-conscious markets - Market expansion: Entry into jurisdictions with strict data localization requirements - Partnership access: Eligibility for privacy-sensitive collaborations - Innovation acceleration: Reduced compliance friction for new products
SECTION V: Technical Challenges Ahead
Zero-knowledge governance is promising but not without challenges that must be addressed for mainstream adoption.
- Computational Overhead
Generating and verifying zero-knowledge proofs requires significant computational resources. While efficiency has improved dramatically—modern ZK schemes are orders of magnitude faster than early implementations—they still introduce latency and cost compared to simple data verification.
Mitigation: Hardware acceleration, proof batching, and continued algorithmic improvements are reducing overhead. For many governance use cases, the computational cost is acceptable given the privacy benefits.
- Complexity and Usability
Zero-knowledge cryptography is mathematically sophisticated. Implementing it correctly requires specialized expertise that many organizations lack.
Mitigation: Open-source libraries, managed services, and standardization are making ZK technology more accessible. Organizations don’t need to become cryptographic experts—they need to know how to integrate proven solutions.
- Verification of the Verifiers
If zero-knowledge proofs replace data disclosure, how do we verify that the proof systems themselves are trustworthy? A compromised proof generator could produce false proofs that appear valid.
Mitigation: Open-source implementations, formal verification of cryptographic protocols, and multi-party computation approaches can provide assurance. Transparency and auditability remain essential.
- Quantum Computing Threats
While current ZK schemes are secure against classical computers, quantum computers could potentially break some cryptographic foundations. Post-quantum cryptographic research must continue to ensure long-term viability.
Mitigation: NIST and other standards bodies are actively developing post-quantum cryptographic standards. ZK systems should be designed with algorithmic agility to enable future upgrades.
- Interoperability and Standards
For zero-knowledge governance to work at scale, proofs must be portable across systems, jurisdictions, and use cases. Fragmentation into incompatible proprietary systems would undermine the entire approach.
Mitigation: International standards development, open-source reference implementations, and regulatory harmonization are essential. Early movers should prioritize interoperability over competitive lock-in.
CONCLUSION: The Architecture of Trust
We’re at a pivotal moment in the evolution of digital governance. The technologies for comprehensive surveillance are mature and deployed. The technologies for cryptographic privacy are emerging and powerful.
The direction we take will be determined not by technical inevitability, but by choices—choices made by policymakers, business leaders, and technologists.
Zero-knowledge governance offers a third path between the false dichotomy of surveillance and exclusion. We don’t have to choose between comprehensive data collection and inability to verify claims. We can have verification without vulnerability, compliance without exposure, personalization without privacy sacrifice.
For Policymakers: Invest in ZK infrastructure as public goods. Create regulatory incentives for privacy-preserving architectures. Lead international standardization efforts.
For Business Leaders: Evaluate where your organization accumulates unnecessary data liability. Pilot ZK solutions in high-value use cases. Position your organization ahead of the privacy curve.
For Technologists: Build the tools that make zero-knowledge governance practical and accessible. Contribute to open-source projects. Educate stakeholders about cryptographic privacy possibilities.
The Future
In a zero-knowledge future, the power dynamics of the information age shift fundamentally. Institutions can verify without knowing. Citizens can participate without exposing. Trust is built on mathematics rather than promises.
This isn’t a retreat from accountability—it’s an advance toward a more sophisticated form of accountability that respects human dignity while enabling collective coordination.
The question isn’t whether zero-knowledge governance will emerge. The question is who will lead its emergence—and who will be left scrambling to catch.